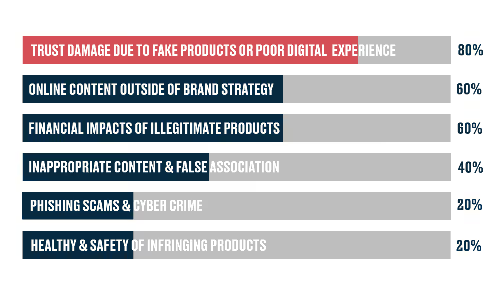
The business models and tactics deployed to hijack businesses' digital channels have become increasingly sophisticated – it’s critical that your team is equipped with the tools and knowledge to remain one step ahead.
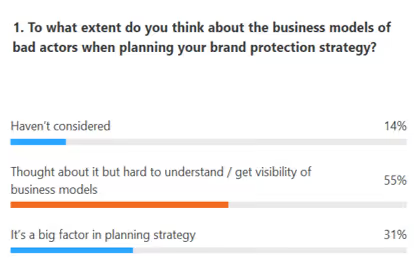
In a poll of Brand Protection professionals 69% stated that when planning their strategy, they either haven’t considered the business models of bad actors or find it hard to understand / get visibility of them.
By building an understanding of bad actors' operating models and uncovering their online networks, brands can maintain consumer trust and maximize the opportunity offered by e-commerce.
Part 1: The threats posed by bad actors online to your business and its consumers
The business models deployed by bad actors most often mimic those of legitimate businesses. Bad actors will also often share the same strategic considerations when they go to market and promote products, utilizing the same digital channels and tools.
The changing online and commercial environment changes the way they adapt, like any business. This is also true when enforcement activity changes their behavior.
Seasonal, trend, and enforcement-based changes in bad actors’ behavior
Bad actors’ behavior is constantly changing in response to events that can impact their sales and ability to operate.
“Changes I commonly observe can be based on similar things to legitimate business: seasons/holidays/trends in the social environment. Bad actors also change as a reaction to enforcement.”
Alex Shad, Brand Protection Team Lead, Corsearch
With Seasonal events such as Easter, Halloween, and Christmas, bad actors will emulate genuine brand behavior on social media, marketplaces, and websites. With cases of phishing, fraud, and impersonation, bad actors attempt to make their social posts and websites appear genuine to trick consumers. They will also combine this with the use of redirects and other entities that look legitimate to divert consumers.
Bad actors will also react to the social climate. For example, they started producing face masks during the coronavirus pandemic – as seen in this network example.
Enforcement is also a key driver, with behavior depending on issue type:
- Fraud/impersonation – enforcement is more likely to scare bad actors into hiding. They will depopulate enforceable pages and then repopulate very quickly without notice to disseminate scams. They may also set up personal profiles to later populate if they are expecting enforcement on pages that are currently live.
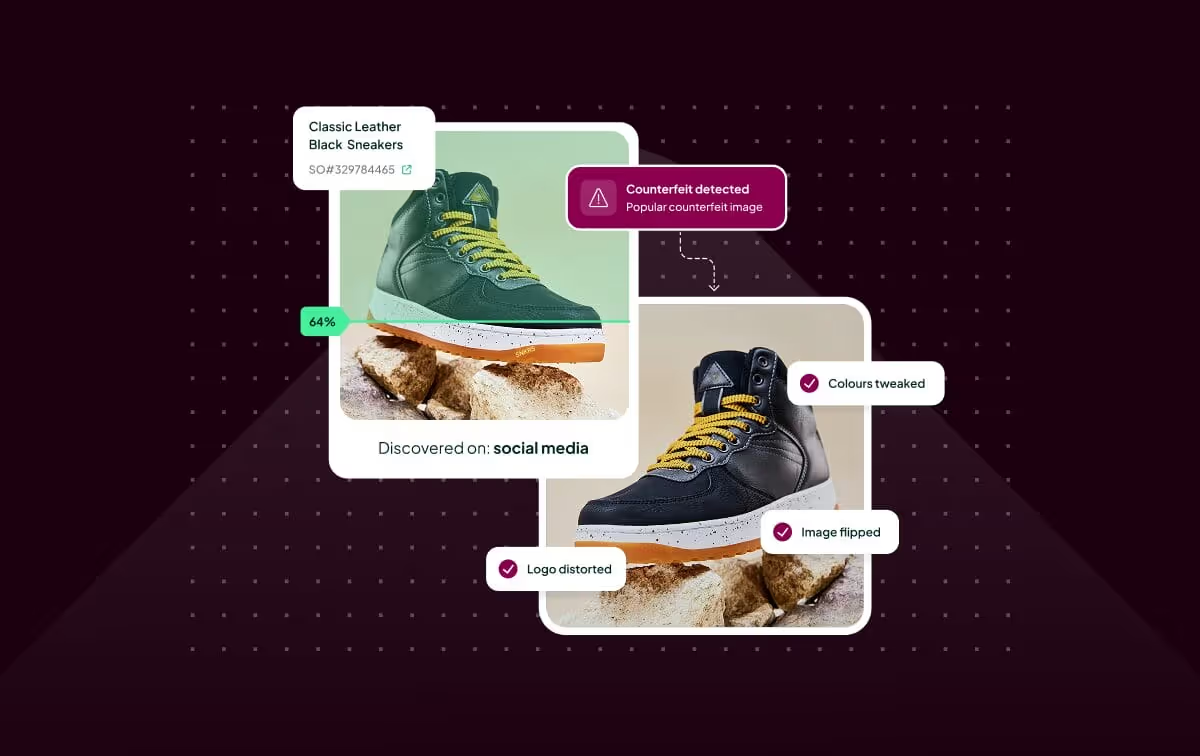
- Traditional trademark infringement – After enforcement, bad actors are more likely to change the way in which they infringe as opposed to changing their business model. The seller may blur over the infringing elements of images or appear to cease the sale of certain products.
Bad actors are often agile operators that adopt emerging platforms
Bad actors can be more dynamic than legitimate businesses at entering new markets and deploying new technology as they have lower barriers to entry. Counterfeiters, in particular, make use of new emerging platforms and have used influencer culture to their advantage.
TikTok, a user-generated content (UGC) platform that has enjoyed huge growth over the last year, is a good example – it has seen over 2 billion downloads in it’s first 4 years since launch, with Q1 2020 seeing over 315m downloads alone. TikTok’s primary audience is younger consumers, who are quicker to adopt newer media formats. Bad actors have latched onto this platform and often use influencers, who lend an aura of authenticity, to promote their goods to large swathes of consumers.
Bad actors are one step ahead in reacting to market trends
Bad actors will also often be one step ahead of legitimate companies in reacting to market trends. An example of this is product unboxing videos – bad actors sometimes enlist the help of prominent influencers on platforms such as TikTok, Instagram, and YouTube to unbox their counterfeit products, highlighting key features and build quality.

When reacting to wider market trends, they do not adhere to rules, regulations, or legal frameworks, meaning they can create and market new product lines far faster than legitimate companies.
Part 2: The models used to capture consumers, and how to disrupt them
We will look at 3 different types of network to illustrate how they are structured and how you can tackle them:
- Simple network: marketplace seller connected by WeChat
- Traditional counterfeiting network selling luxury watches
- Multichannel network selling flavored vaping liquids
1. Simple network – Shopee storefronts seller connected by WeChat
In this example, Corsearch analysts discovered a network selling counterfeit goods that pose a health risk to consumers.
Key features of the network:
- Marketplace seller found to be offering infringing items which posed a health risk to consumers
- WeChat ID connected the account to 32 other storefronts on the same platform
- Auditing these connected storefronts could reveal further issues for the brand

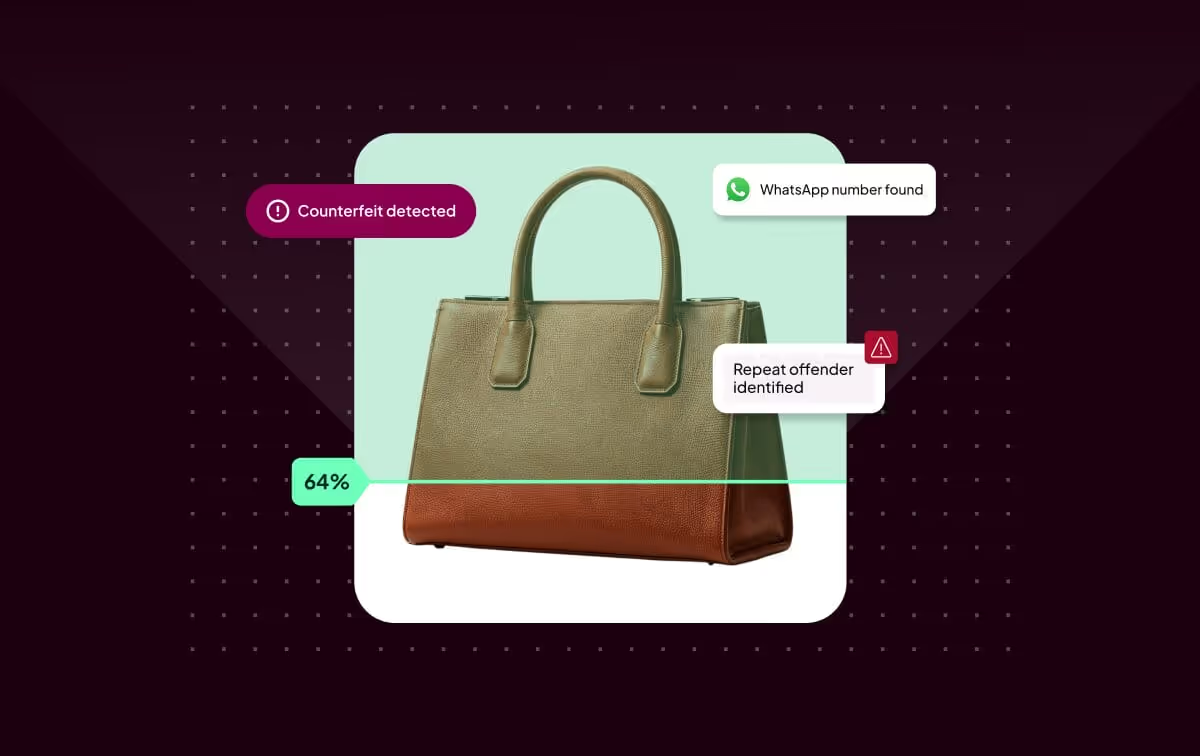
The network is comprised of multiple Shopee storefronts all connected by one single WeChat account – without using Network Analysis technology, these storefronts would have been encountered one by one without the link ever being made, removing the possibility for coordinated enforcement causing max disruption.
Using this link, Corsearch analysts can search and ‘audit’ each linked storefront and screen these for similar infringements or references to the relevant brands. If other infringements are found, these can be collected for enforcement as one notice through the Shopee webform. An additional benefit of coordinated enforcement on individual sellers is the increased chance the platform would proactively deactivate the whole storefront.
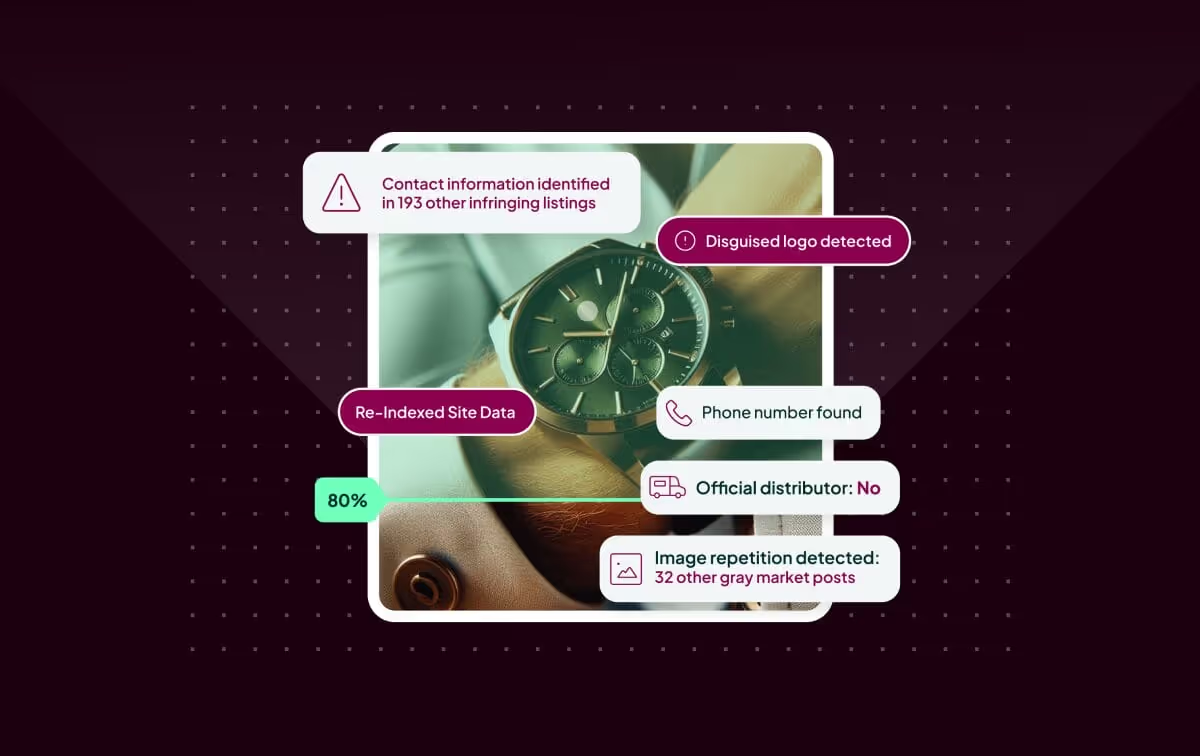
2. Large-scale network selling counterfeit luxury watch network
In this example, Corsearch discovered a typical counterfeiting network offering luxury watches predominantly via websites. The network was multinational in nature, with a global supply chain which centered on China.
Key features of the network:
- Large scale network containing 216 websites connected by 8 common email addresses (3 China-based and 5 international)
- These networks primarily use traditional search methods to attract traffic
- Targeted multiple brands owned by a number of different businesses, indicating a broad network (other brands targeted: Rolex, Breitling, Timberland, UGG)
Coordinated action against all of the entities within the network is one method to effectively disrupt its operation. With most of the network’s customers arriving via organic search, Google’s URL delisting tool could also come in to play to starve the network of its traffic source. Equally, due to the large scale of the network, offline action with legal partners would also be an effective strategy to tackle the perpetrators.
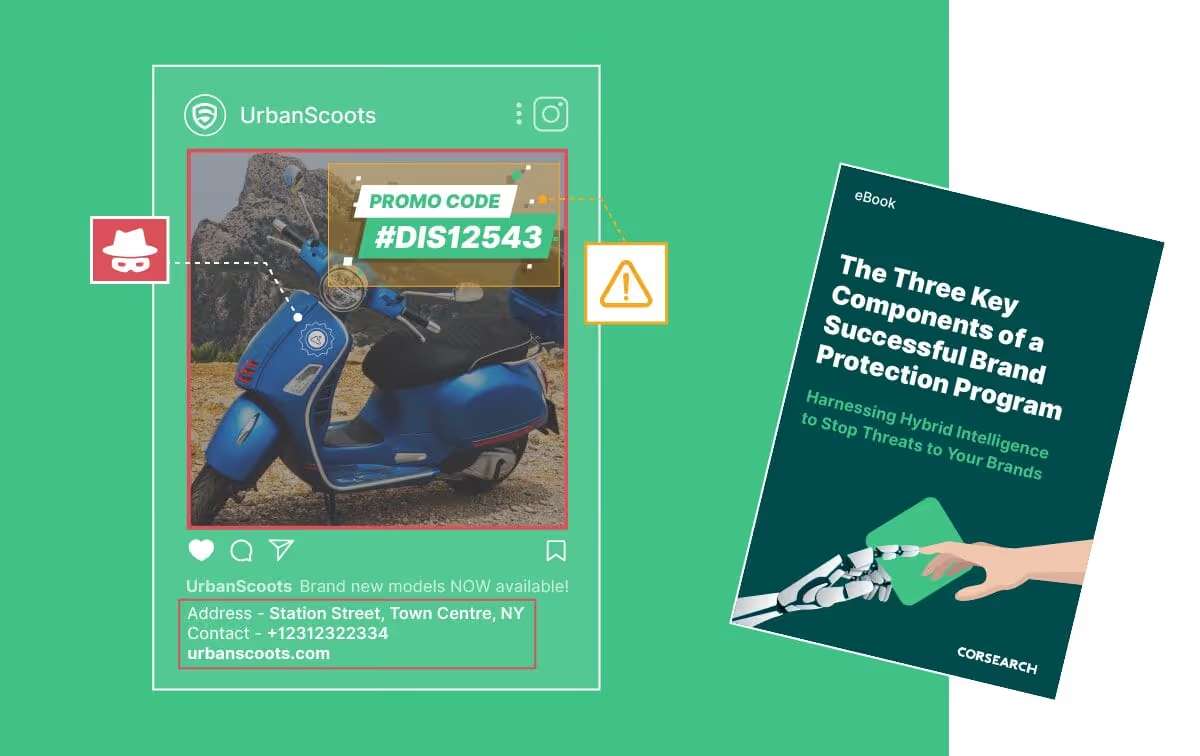
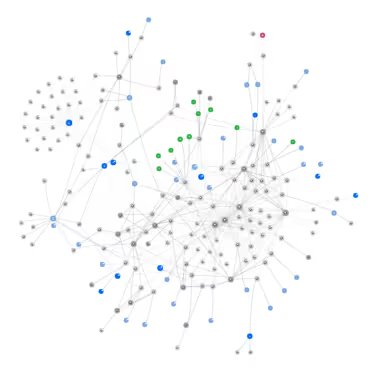
3. Multichannel Network selling vaping products
In this example, vaping liquid products were sold via websites and marketplaces with promotional pages on social media.
Key features of the network:
- Complex network with multiple storefronts and websites
- Domains connected by a company that supports website & online store set up and synchronization
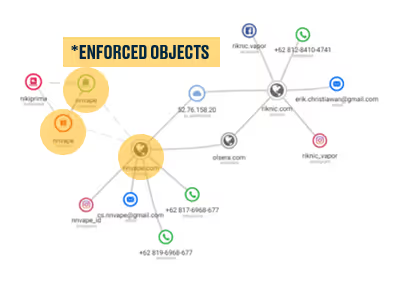
Connections made by Network Analysis technology allow for all marketplace listings, social media posts, and domain URLs to be enforced at once, leaving the bad actor with no opportunity to change product listings. The Domains that are connected by the website set-up company can then be forwarded to the Investigations Services team to build further intelligence.
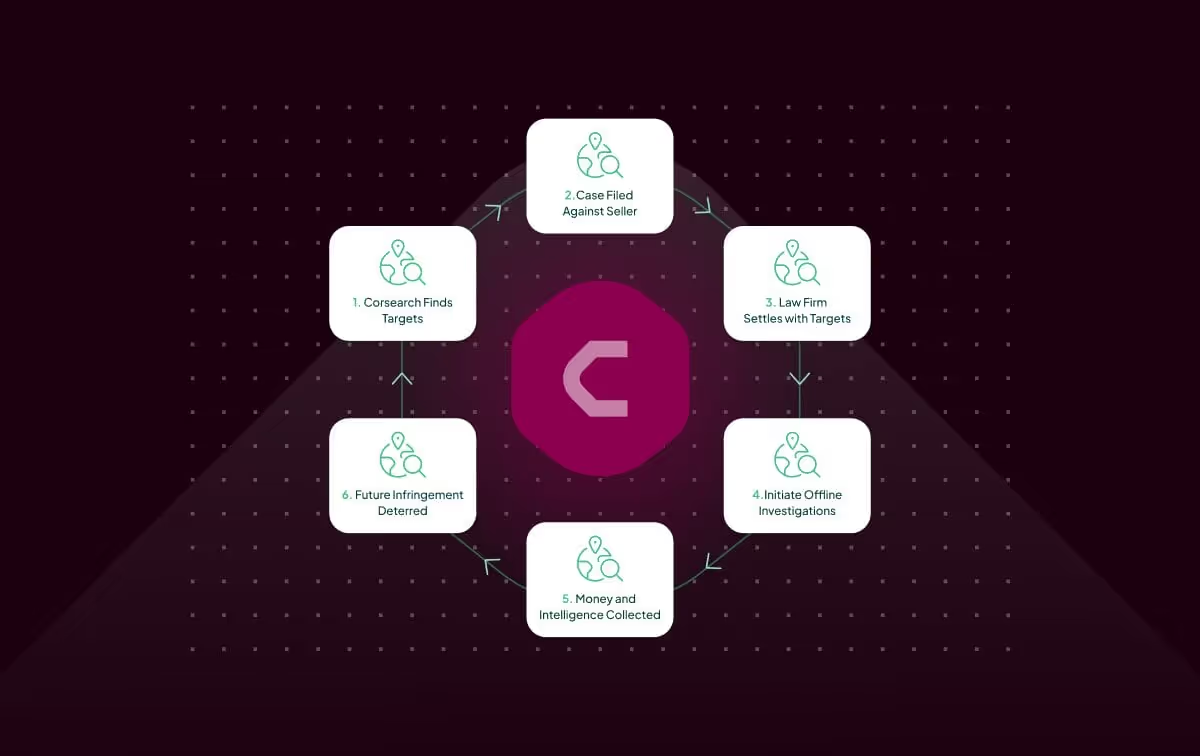
Corsearch Case Study: Offline action disrupting counterfeit jewelry network in China
One core avenue to dismantling bad actor networks is coordinated offline action in liaison with local authorities and law enforcement agencies.
In 2018, a counterfeiting ring that peddled high-value jewelry (average price $8,000) across popular online marketplaces was discovered by Corsearch’s analysts. Test-purchases were used to gather identifying information on the perpetrators, with the wider case being built using data gathered from Taobao, Weibo, and WeChat. Subsequent offline action led to over 50 arrests and seizure of products across seven addresses.
Multilateral action is key to more effective offline action. In China, the close relationship between CBBC (China Britain Business Council) and platforms such as Alibaba now make offline investigations easier to undertake.
Part 3: How Network Analysis technology can help you address these threats effectively
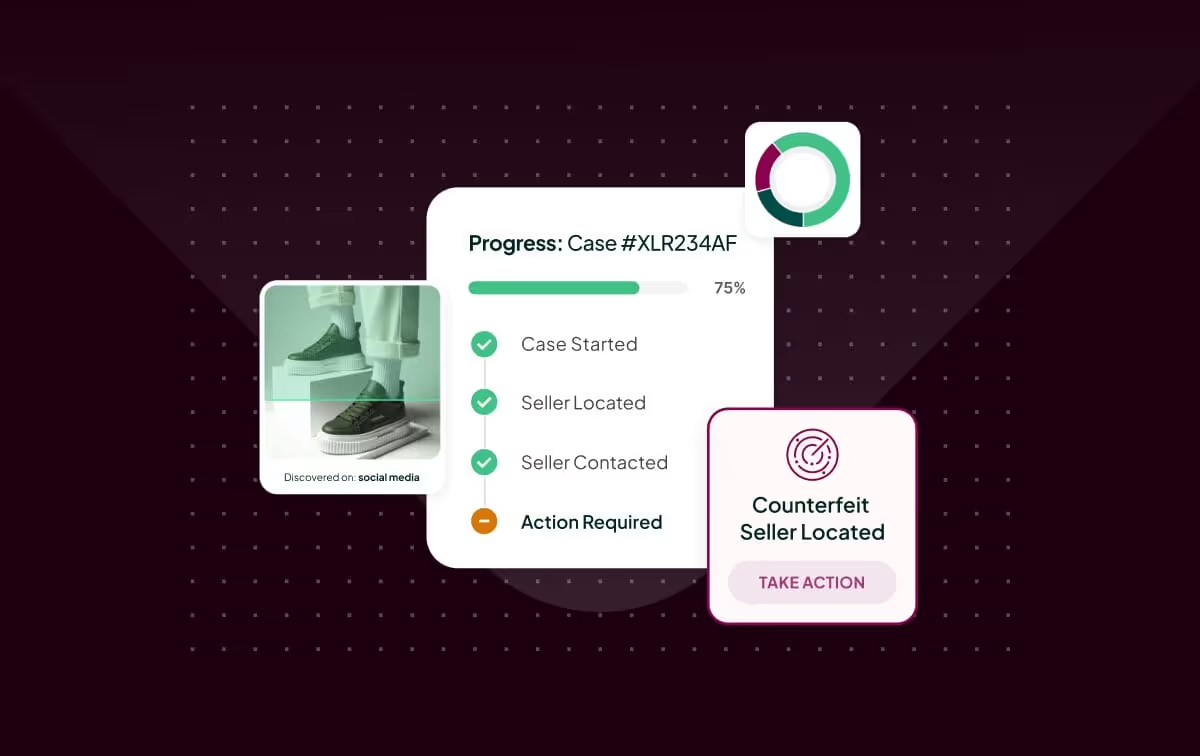
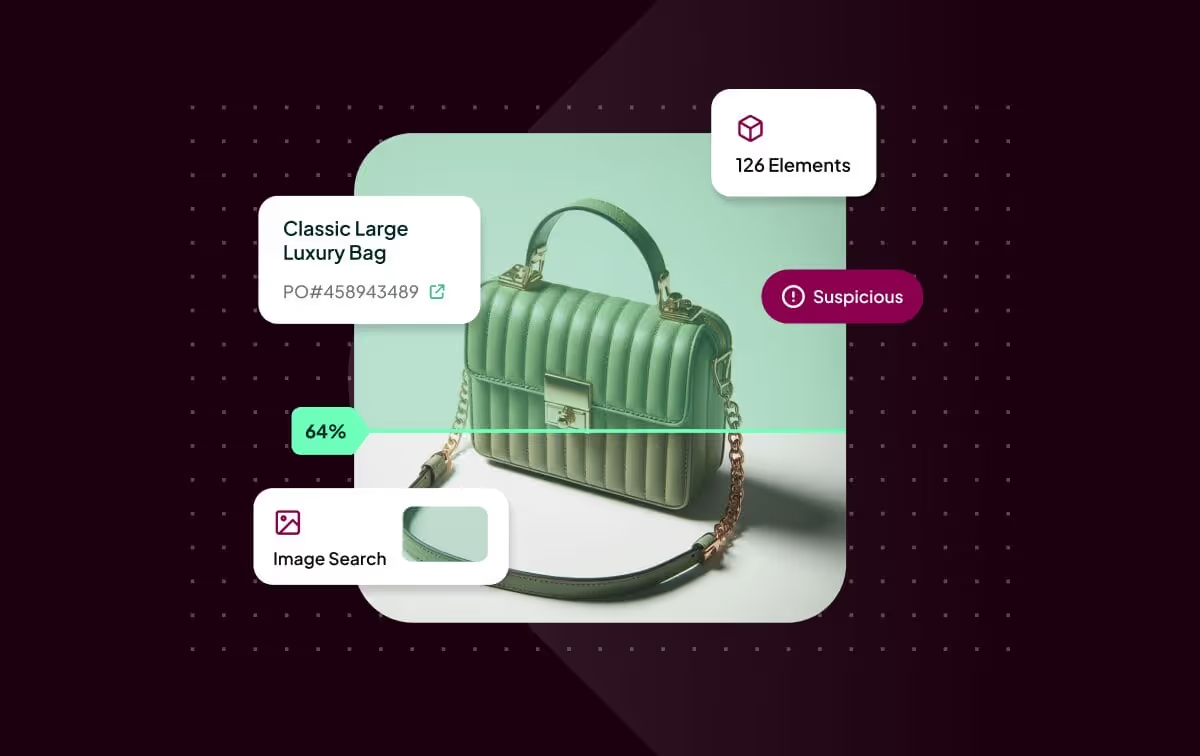
Network Analysis is a core module of Corsearch’s Brand Protection platform that powers a strategic approach to tackling networks. By connecting infringing entities across channels such as websites, marketplaces, and social media – and matching them against online and offline identifiers – Network Analysis gives you full visibility of the risks to your brands, prioritizes them by threat level, and provides you with the insights to act on them at scale.
There are four key components to Corsearch’s Network Analysis technology that enable you to tackle the most damaging threats to your business:
1. Good quality data = Meaningful networks
- Processes for cleaning and validating data before networks are built
- Algorithms to make networks more meaningful, e.g. take out nodes with too many links
- All useful data points extracted, both structured and unstructured
- Inferred links based on similarities – helps uncover potentially connected nodes
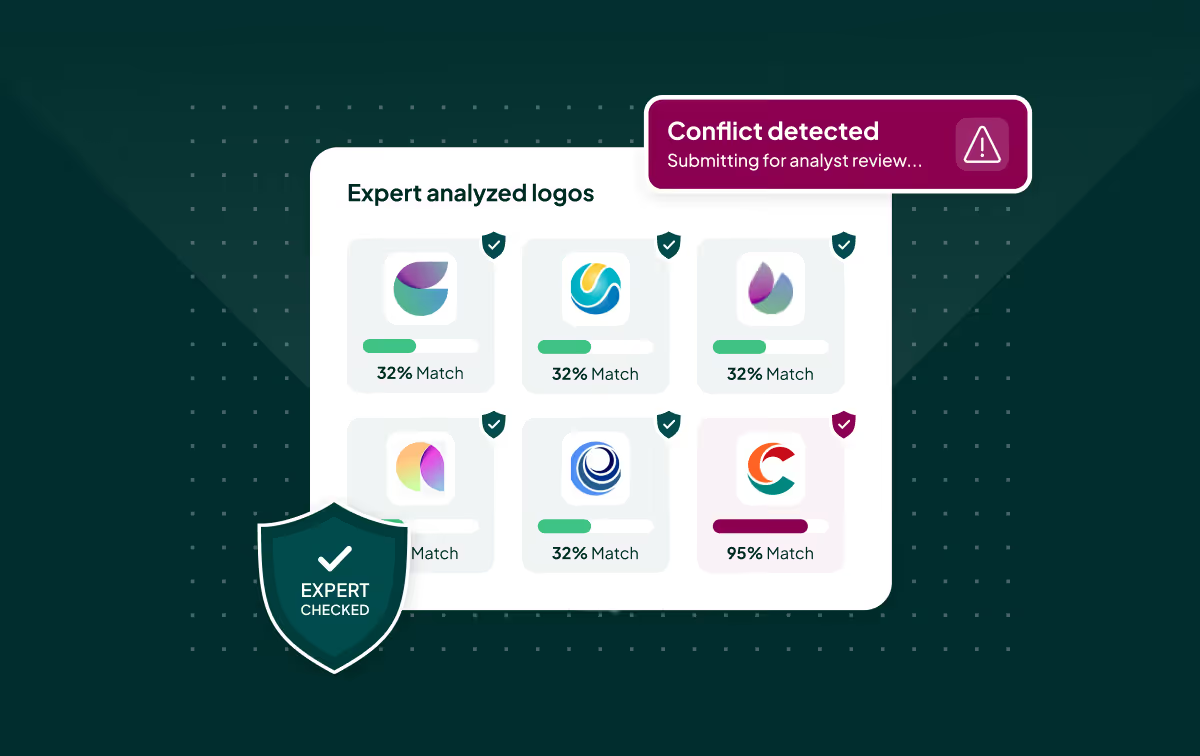
2. Contextualized threats in the 'universe' of networks
- Threat score to prioritize and assess each network
- Take into account popularity, action taken and the risk from the network’s component parts
3. Tools to search, manipulate and edit
- Search and filter clusters on a wide variety of data points
- Compare networks to understand the bigger picture
- Add and remove nodes and links to build out your online and offline intelligence picture
4. Impactful inforcement from the network view
- Identify key enablers to dismantle all or part of the network, as your strategy directs
- Tackle the whole network and see how it responds
When to use Network Analysis within your workflow
The tool has the potential to be used as both a principal resource for online action and a supplementary resource for further enforcement. Brand owners can filter through high-risk networks and networks that include tagged objects. This includes checking connections made with official entities.
Brand owners can then screen, tag and enforce infringements outside of the tool and then filter for those tags and enforcements in Network Analysis. This can open the door to a possible string of previously unseen connections and sellers to be targeted.
This is beneficial if a team needs to focus on multiple online issues at any one time. It is also useful where issues are more ‘trends’ that spread across a number of sellers and are therefore not specific to a single bad actor.
For novel issues or issues where sellers are known to change their behavior quickly, the preferred workflow would be enforcing all infringing items in a network at once.
Request a demo
Network Analysis gives you insight into the different networks that are hijacking your brand and exploiting consumers. By building a full picture of these networks and prioritizing based on threat, we can drive enforcement and investigations in a more strategic, impactful way.
If you would like to find out more about our Network Analysis technology and how it can empower your team, request a demo below.
See how PharmaCheck™ accelerates name qualification
From early-stage screening to post-clearance checks, we help you move faster with confidence — while avoiding missteps new, and help you move forward — faster.






.svg)
.png)







.svg)


.avif)

.avif)